News
The NSA's Weirdest Code Names
In light of the latest revelations courtesy of Edward Snowden — that the NSA snooped on Muslim Americans and snared way more regular people than terrorists — we thought we'd take a look at the weirdest NSA code names revealed by Snowden so far. We were helped by this handy rundown of every NSA program that's been unveiled in the past year by ProPublica.
On Wednesday, ProPublica noted on Facebook that while it had first posted its look at all of the NSA programs a week ago, it's had to update it twice thanks to revelations about new NSA programs, including a program used to monitor some prominent Muslim Americans, some of them who either worked for the U.S. government, never showed signs of being even remotely connected to extremists, or both. Meanwhile The Washington Post reported last week that nine of ten people who showed up in agency-intercepted online conversations included random people who weren't the targets of the NSA's surveillance.
That's all bad enough. But to add to the creepiness factor, the NSA often cloaks its programs in code names that appropriate words from mythology, cartoons, and games and apply them to real-life government snooping, like a bizarrely childish version of the usually intense-sounding CIA cryptonyms.
So here's a rundown of the seven weirdest NSA code names, according to a highly scientific (gut) analysis. Ranked from weird to weirder:
1. Gilgamesh
Gilgamesh was a king of Uruk, in what's now Iraq. He's also the star of the Epic of Gilgamesh , one of the oldest stories in existence. But at the NSA, the name Gilgamesh — clearly a nod to the project's geographic focus — means a system through which Predator drones home in on a cell phone's SIM card the agency believes belongs to a target, according to The Intercept.
As the drone circles, the device locates the SIM card or handset that the military believes is used by the target.
More like Gilgasketch, amirite?
2. Royal Concierge
This aptly-named program tracked "potential Diplomatic hotel reservations," according to Germany's Der Spiegel. Its existence was leaked by Snowden, but it was actually run by the British GCHQ. Like the rest of us, they probably wanted to know where Kate Middleton is staying in her travels abroad. (It more than likely targeted foreign diplomats, not Brits, actually.)
From the paper:
The top secret program carries the codename "Royal Concierge," and has a logo showing a penguin wearing a crown, a purple cape and holding a wand. The penguin is apparently meant to symbolize the black and white uniform worn by staff at luxury hotels.
Really, GCHQ? A penguin?
3. Angry Birds
Speaking of birds, here's another fun NSA code name that hides its creepy purpose. The program looked for vulnerabilities in "leaky," insecure apps that would allow a third party access into a smartphone. Another name for a similar program? Candy Crush.
4. SecondDate
This one allowed the NSA to get in the middle of a server's communication with a client, according to The Intercept. It could be used on specific people or to attack many people with malware, the site reported.
5. Squeaky Dolphin
This oddly-named program is one of the more alarming on the list because it directly targets social media accounts. The Squeaky Dolphin is actually a "real-time user and data collection initiative that monitors YouTube views, Facebook likes and Blogspot or Blogger visits for analysis," BGR reports.
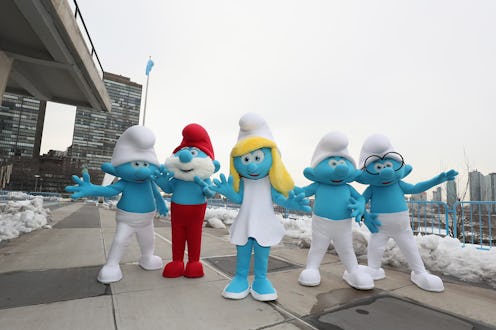
6. The Smurfs
NoseySmurf, TrackerSmurf, DreamySmurf, and ParanoidSmurf are the kinds of specific phone hacking programs Snowden talked about in his recent interview with Brian Williams. The programs help the NSA get inside cell phones and do things like turn on the microphone to overhear their owners' conversations, ProPublica and The Guardian say. They can also manipulate the phone's use of battery power and track the phone's location.
7. EgotisticalGoat/EgotisticalGiraffe
These two programs work to track down people who are going out of their way to avoid being tracked using Tor programs. (Tor is supposed to prevent outsiders from tracking your browser activity.) No word on why they're named after ungulates with personality deficits.
Images: NBC; Getty Images (6)